When the Target Defends Itself: Lessons from a Hardened Wi-Fi Assessment
Sometimes the most valuable security lesson is not from breaking in — but from failing to.
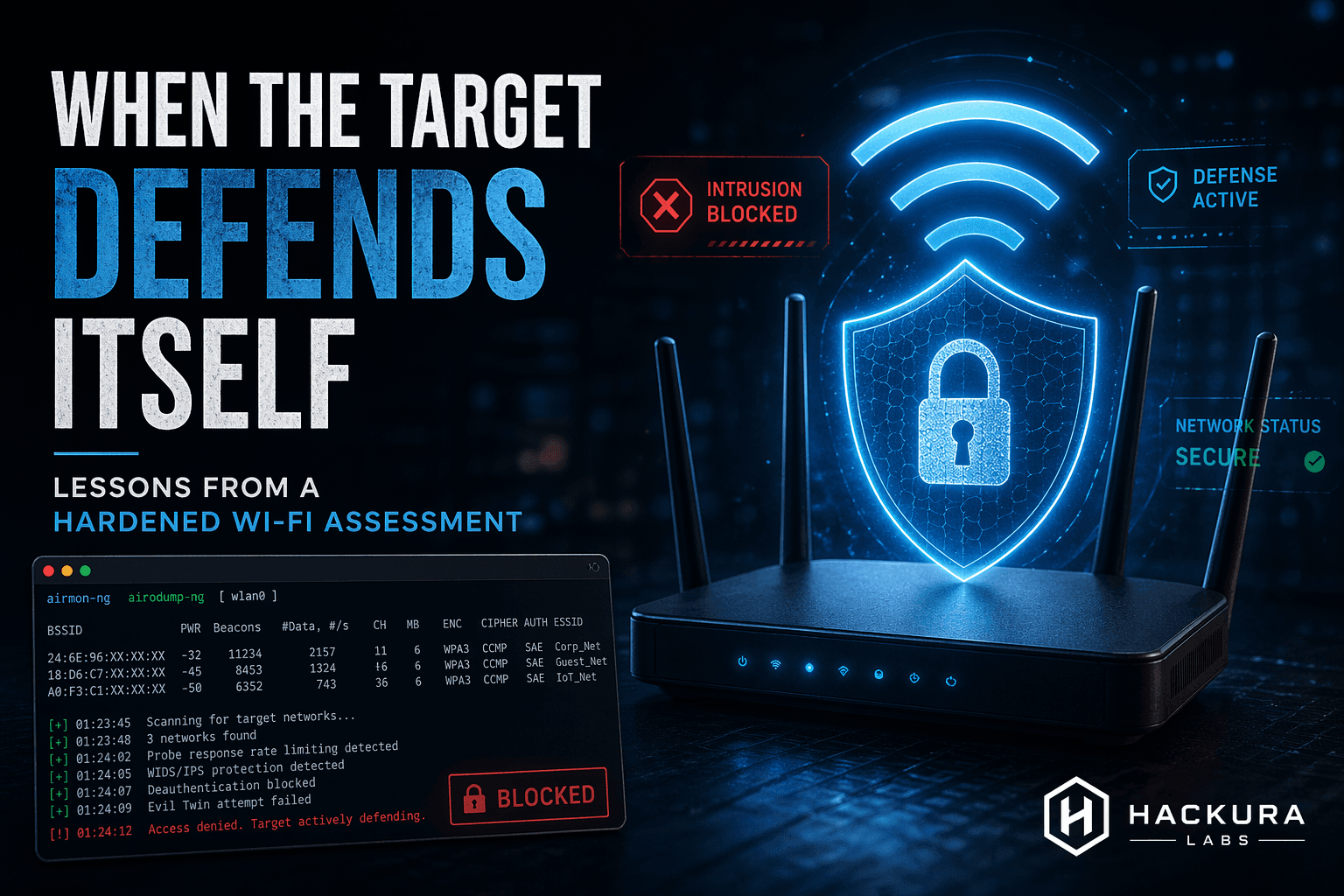
Recently, during a controlled wireless security assessment, I encountered something interesting:
The target didn’t just resist attack.
It appeared to defend itself.
And that changed the exercise from “Can this network be broken?” into something much more important:
What makes a wireless network resilient against modern attacks?
The Assumption We Often Make
People often assume Wi-Fi security failures are inevitable.
- Weak passwords
- Misconfigurations
- Legacy protocols
Sometimes that is true.
But well-defended wireless environments tell a different story.
This network exposed very little.
Minimal leakage.
No obvious attack surface.
Behavior that suggested protective controls were actively reducing exposure.
That alone was a lesson.
Security Wasn’t One Thing — It Was Layers
Strong wireless security rarely comes from a single control.
It comes from layered defense:
- Strong authentication
- Modern encryption
- Proper segmentation
- Attack surface minimization
- Rogue activity detection
- Automated protective controls
- Hardened configuration
Defense in depth works on Wi-Fi too.
The “Failure” Was Actually Success
Not breaking through was useful.
Because it forced a better question:
Why did the defenses hold?
That’s where learning happens.
Security isn’t only studying compromise.
It is studying resistance.
Modern Wireless Defense Is Evolving
What stood out most was how modern protections can reduce visibility to attackers.
Hardening today is no longer just setting a password and enabling WPA.
It is active defense.
- Detection
- Response
- Adaptive protection
- Increasingly, automation
That matters.
Because defenders need to know protection is possible.
Takeaway
The exercise reinforced something simple:
A well-defended network should be difficult.
If it is easy, something is wrong.
Sometimes the most impressive result in a security test is discovering the controls actually work.
And honestly—
that is a win.
Final Thought
In cybersecurity, success is often measured by what gets exploited.
Sometimes it should be measured by what withstands exploitation.
Those lessons may be even more valuable.
Published on Hackura Labs
Research • Defense • Security Engineering